APPLICATION SECURITY TESTING: SAST, DAST, IAST, and RASP

Security testing is improving faster than any other security market in IT Systems, It is a type of Software testing that opens vulnerabilities of the system and resolves that the data and resources of the system are protected and guarded against possible thieves. It ensures that the software system and application are free from any threats or risks that can affect a loss. Experts determine that about 90% of security conflicts are the result of attackers exploiting known software errors.
Security testing of any system is focusing on finding all potential loopholes and vulnerabilities of the system which might appear in the loss of information or fame of the organization. Application testing tries to manage out the possibility of faulty code.
As a result, it detects any errors from the beginning and helps developers, to prevent errors from reaching the final version of the software. It is essential to keep a high level of security, continuously testing the functioning applications.
Principals of the Software Testing
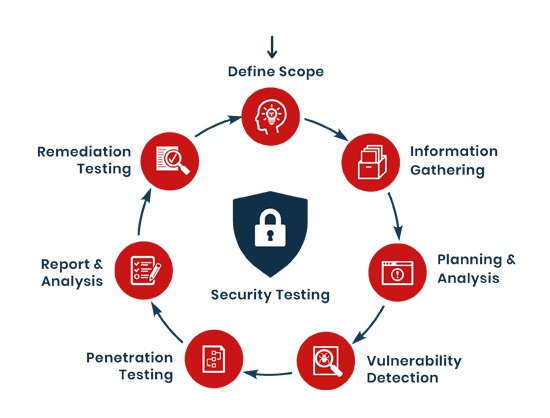
Focus Areas in Security Testing

Types of Security testing

Application Security Testing Tools
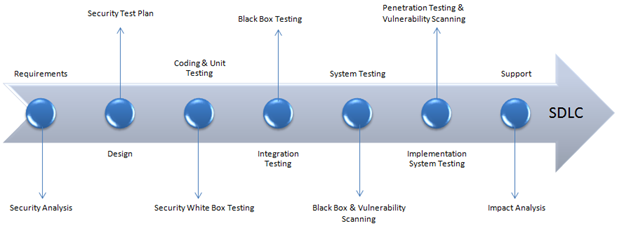
Several marketing Testing Tools available which can help you to design and develop a highly secure application with error-free. We will analyze various automated solutions that can assist developers and help testers to identify vulnerabilities in their code at different stages of the Software Development Cycle.
SAST (Static application security testing)
Static Application Security Testing also known as source code scanners or white-box testing tools, it is inspected source code or binaries and gives feedback on possible vulnerabilities. These tools are designed to examine the source code of an application and spot potential issues during the development phase of the SDLC
Advantages of SAST
- Mending vulnerabilities is more competitive since it comes earlier in the process.
- Analyzes 100% of codebase more speedily than possible by humans.
- Ingested before the application is in production and without execution of the program
- Provides real-time feedback and graphical representations of issues uncovered.
- Looks out the exact location of vulnerabilities and query code.
- Offers customized reports that can be exported and tracked with dashboards.
- Automation is possible.
- Broad Programming language support.
Disadvantages of SAST
- Needs to synthesize data to test code leading to false positives.
- It cannot detect runtime issues alike authentication issues or server misconfigurations.
- Language dependence produces tools difficult to build and maintain and requires a different tool for each language used.
- Not much at understanding libraries or frameworks, like API or REST endpoints.
- Helpless to check calls or most argument values.
- Poor accuracy: 53% of issues detected are non-existent (false positives)
- Antiquated technology that has not evolved.
- SAST code analyzers have no visibility of the execution flow.
- The output is a static report that quickly becomes outdated.
- They often require some customization or tuning.
- Not applicable to systems in the Production stage.
SAST tools are helpful technology but not a substitute for other methods. Developers would appropriate a combination of techniques during the process to conduct assessments and catch flaws before going into production.
To overcome some of these limitations a different testing approach called DAST can be used.
DAST (DYNAMIC APPLICATION SECURITY TESTING)
DAST is accommodated to a waterfall development approach, agile and DevOps development can benefit as well. It is a black-box analyzing testing method, which means DAST tools don’t have access to the source code. Alternatively, they outside examine a running web application, assuming a real attack just similar to a penetration test. The purpose is to recognize how the application reacts to different shooting vectors and identify possible vulnerabilities.
“Dynamic scanning is something that you apply during the testing and QA phase of the SDLC.
Advantages of DAST
- Identify and Highlights vulnerabilities issues like authentication, memory leaks, weak ciphers, and server configuration.
- Recognize vulnerabilities not just in the web application, but in infrastructure as well.
- Language independent.
- Evaluates the whole application and system.
- Tests memory consumption and resource use.
- Tries to break encryption algorithms from outside
- Verifies authorities to ensure isolation of privilege levels.
- Checks for cross-site scripting, SQL injection, and cookie manipulation.
- Tests for vulnerabilities in third-party interfaces.
- Comprehends arguments and function calls.
- Fit good support for manual pen-testing.
Disadvantages of DAST include:
- Doesn’t evaluate code itself or highlight vulnerabilities in code, only resulting in issues.
- Cannot identify access control issues.
- During the active scanning phase, the tool sends attack payloads that may modify, delete, or corrupt existing application data.
- Cannot pinpoint the exact location of the issue in the codebase.
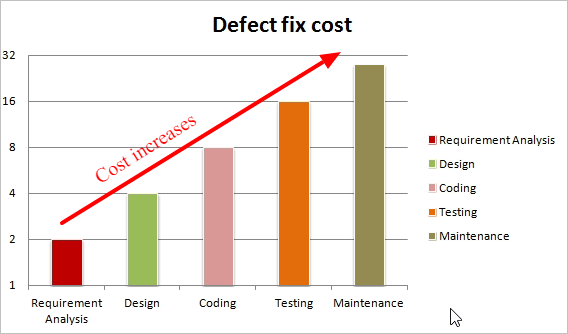
- Used after development is complete so fixing vulnerabilities is more expensive.
- Large projects require custom infrastructure and multiple instances of the application run in parallel.
The selection between adopting DAST or SAST analysis tools mainly depends on what you are trying to accomplish. SAST provides developers with educational feedback, while DAST gives security teams quickly delivered improvements. DAST should be used less frequently and only by a dedicated quality assurance team but it may not cover 100% of the application, which means they can miss some vulnerabilities in less-obvious features.
IAST (Interactive Application Security Testing)
It is a combination of static and dynamic techniques tools to improve testing.”
IAST has an “agent-like” approach, meaning agents and sensors are appeared continually to analyze the functioning application during automated testing, manual testing, or a mix of the two. In other words, IAST tools examine the source code of the web application while it is working to identify more vulnerabilities with a lower rate of false positives.
According to the research firm Gartner, ” next-generation modern web and mobile applications require a combination of SAST and DAST techniques.
Advantages of IAST
- Able to integrate with continuous integration (CI) and continuous development (CD) tools.
- Provides detailed information on the root of vulnerabilities, including code location.
- Can use data collected by sensors about middleware services (web servers, proxies, load balancers, etc.) and configuration options to check for misconfigurations.
- Real-time results provided.
- Allows API testing, good for products using microservices.
- Potential issues are caught earlier so IAST minimizes costs and delays. This is due to the application of a Shift-left approach, meaning it is performed during the early stages of the project lifecycle.
- Promotes reuse of existing test cases.
- Integrates to allow an analysis of source code, runtime control and
- The combination of SAST and DAST functionality allows more accurate results and the identification of a broader range of vulnerabilities.
- Continuous detection, which is DevOps-friendly.
- Truly Plug&Play, no configuration or tuning is required.
- Communication with task management systems creates interconnected workflows.
Disadvantages of IAST include
- Tools are proprietary, creating a dependence on the supplier for support.
- Limited language support.
- Can slow down the operation of the application. The agents essentially serve as added instrumentation, leading to the code not performing as well.
- IAST tools analyze the features of a web application that are executed. Therefore, the developer has the responsibility to create tests that cover the entire application.
- IAST requires the installation of security sensors and agents within the web application. Depending on the IAST tool, the setup process can be complicated and require the assistance of a specialist.
- It is possible to have compatibility issues between the IAST agent and the technologies used to develop the application.
RASP (Runtime application self-protection)
RASP the evolution of SAST, DAST, and IAST analyzing tools. It combines with applications and investigates traffic and end-user behavior at runtime to block attacks. It means RASP can propose a warning in diagnostic mode and prevent an attack in protection mode, which is done by either stopping the execution of a certain operation or terminating the session. These tools are used after product release so they are more focused on security than testing.
Advantages of RASP include:
- Runs continuous security checks and can respond to attacks with session termination or alerts.
- Integrates with the application, not reliant on network-level protections or remote connectivity.
- It can be easily applied with faster development cycles.
- It allows you to quickly respond to an attack by providing exhaustive analysis and weak locations.
- Has code-level visibility for more comprehensive protection.
- Gives a log of activity for analysis.
- Not language or platform dependent.
- Covers a broad range of vulnerabilities.
Disadvantages of RASP include:
- Can only be used in production.
- Tempting to use as a fallback for patching vulnerabilities, leading to less rigorous pre-release testing.
- By sitting on the application server, RASP tools may have a negative impact on application performance.
- The emerging technology may not be compatible with commands or internal policies, which restrict installing other software, or locked-down services.
- RASP isn’t a substitute for application security testing, as it is incapable of providing comprehensive protection.
Conclusion:
SAST, DAST, IAST, and RASP are vast tools that can complement each other. Ideally, it would be best to use a mixture of tools to secure and ensure better coverage and decrease the risk of vulnerabilities in production. Although of the challenges found in technologies like SAST, DAST, IAST, and RASP, using them can design more secure software and do it in a way that’s faster and more cost efficient than tacking all security testing to the tail of the development process.
Adopting automated tools in the beginning stages can significantly improve and increase security with minimum cost. However, understand and keep in mind that these tools are not expected to be a replacement for all other secure coding practices, but willingly are part of a larger application safety effort.

